Secure Access Service Edge (SASE)
SST SASE was designed and established based on AT&T global SASE architecture and standard. It integrates the advanced hosting SD-WAN services and network security functions with rich Internet access resources to provide customers with one-stop SASE solutions.
- Effective integration of network and security: SD-WAN, SWG, FWaas and ZTNA are effectively integrated to meet the demand of enterprises for dynamic secure access
- Simplification of complexity to reduce comprehensive enterprise costs: the network and security services are integrated into the same vendor (MSP) to reduce the number of hardware and agents on end-user devices;
- Unified management of diverse scenarios, and minimal operation and maintenance: multiple security functions are flexibly deployed to quickly establish an application based network edge security protection system;
- Zero trust network access capability: identity authentication is conducted for visitors to make a precise access control.
Classified Protection Consulting and Value-Added Service
In full cooperation with the professional classified protection evaluation organizations, SST provides enterprise customers with one-stop evaluation, consulting and rectification services.
- Assist enterprises in fulfilling their responsibilities and obligations under cyber security laws and meeting compliance requirements;
- Improve the security protection capabilities of information systems and reduce the risk of system attacks.
DDOS Protection Service
SST provides operator level DDOS security protection products. With the unique large network capabilities of the operator and in combination with multiple protection means, SST monitors, analyzes, traces, and locates attack traffic from a network wide perspective to achieve accurate attack protection.
- Provide T-level protection bandwidth and unique near-source cleaning capabilities of the operator;
- "0" operation of users; "0" equipment deployment of users;
- Provide one-stop secure private line service in conjunction with SST Internet access.
AT&T Secure Web Gateway Service
SST has built a zero trust-based cloud security platform for enterprise customers that establishes a secure connection between users and applications to provide a secure, stable, and efficient access from terminals to enterprise resources in the network.
- Provide the flexible cloud-based subscription services for which the deployment of client devices is not needed, thus reducing one-time investment;
- Support hierarchical grouping management to enable unified management of all sites and facilitate operation and maintenance;
- Provide the ability to access to secure access service edge (SASE) access based on SST SD-WAN technology;
- Provide high-performance no-sensing full traffic checking, with traffic forwarded only once and authentication performed once
Security Information and Event Management (SIEM)
Provide fast and accurate security situational awareness, internal and cloud environment threat detection, and security risk assessment to help clarify threats, conduct investigations, and actively respond to the visibility and analysis technologies required.
- Support both cloud and local deployments;
- Provide flexible and modular subscription services
- Support from professional security operation and maintenance team.
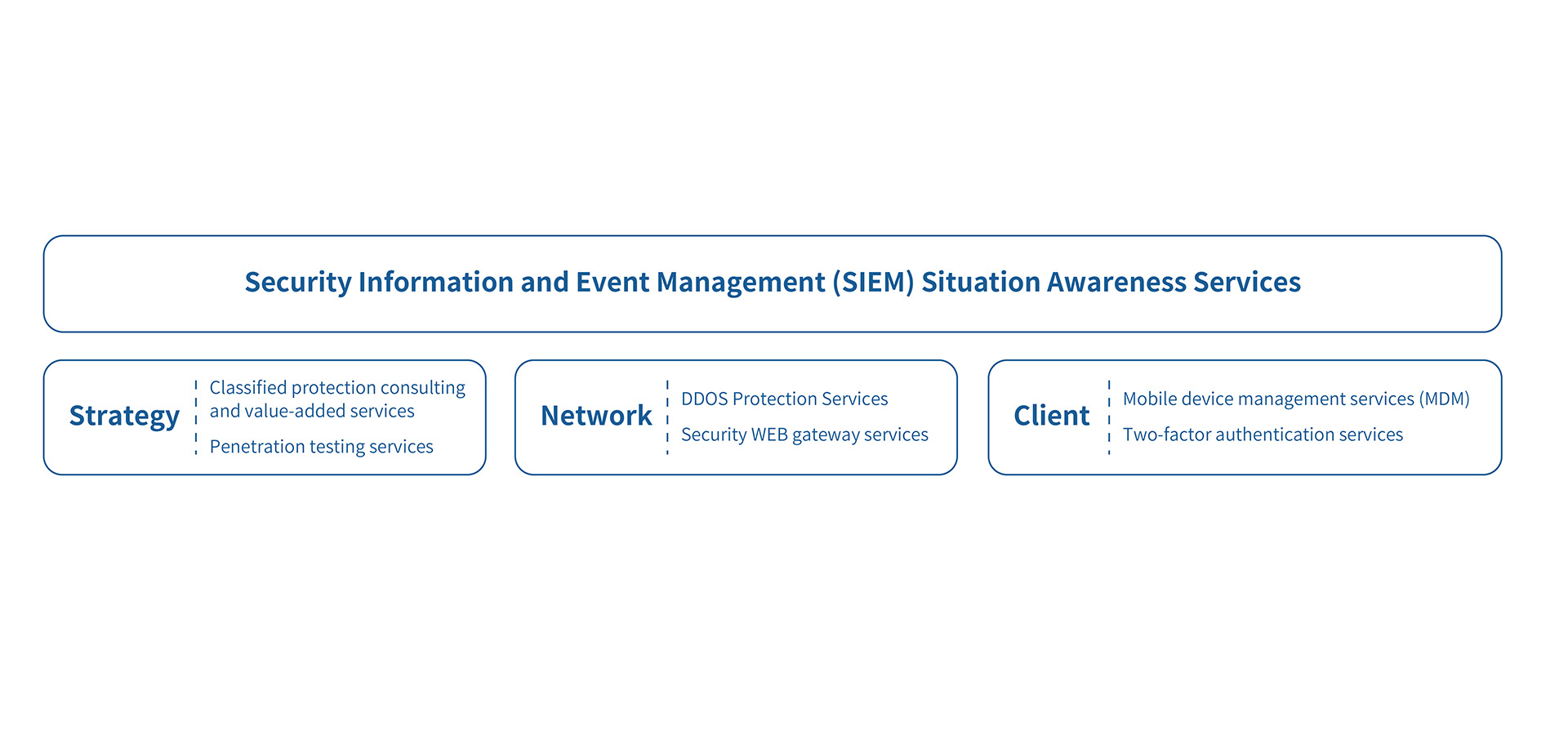
Security Penetration Testing Service
Provide security penetration testing services to detect vulnerabilities in the system and the means that attackers may exploit. Enable enterprise managers to have a clear understanding of the issues the current system is facing.
- Analyze security risks in the runtime environment of information systems
- Identify safety risks and provide repair recommendations and preventive measures;
- Effective review of risk control strategies.



